Aalborg Universitet Charaf, Hassan
... raw data of a generation when it is completely decoded. Thirty seconds after transferring all bytes from a generation, it will be considered obsolete, and its data buffer will be deleted from memory. This way we can avoid memory leaks, which would quickly accumulate in our application during the pla ...
... raw data of a generation when it is completely decoded. Thirty seconds after transferring all bytes from a generation, it will be considered obsolete, and its data buffer will be deleted from memory. This way we can avoid memory leaks, which would quickly accumulate in our application during the pla ...
www2.unescobkk.org
... Intranet is an internal corporate network that provides access to information and allows communication limited only within an organization. ...
... Intranet is an internal corporate network that provides access to information and allows communication limited only within an organization. ...
tg04 - CE Sharif
... LAN technology File server. A repository of various software and data files for the network, which determines who gets access to what and in what sequence Network interface card. Hardware that specifics the data transmission rate, the size of message units, the addressing information attached to ea ...
... LAN technology File server. A repository of various software and data files for the network, which determines who gets access to what and in what sequence Network interface card. Hardware that specifics the data transmission rate, the size of message units, the addressing information attached to ea ...
[2017 New] 100-105 New Questions For Passing The 100
... protocol specific packets. Access lists can be used in a variety of situations when the router needs to be given guidelines for decision-making. These situations include: Filtering traffic as it passes through the router To control access to the VTY lines (Telnet) To identify "interesting" traffic t ...
... protocol specific packets. Access lists can be used in a variety of situations when the router needs to be given guidelines for decision-making. These situations include: Filtering traffic as it passes through the router To control access to the VTY lines (Telnet) To identify "interesting" traffic t ...
Pino
... Reference designs are available for both 2.4GHz (Nordic nRF51822 ) and Sub-Ghz (Silicon labs EFM32LG+Si446x). More platforms will be released in Q1/2015. Evaluation kits are available for selected customers. Kit includes graphical diagnostics tool which is very useful to understand the network behav ...
... Reference designs are available for both 2.4GHz (Nordic nRF51822 ) and Sub-Ghz (Silicon labs EFM32LG+Si446x). More platforms will be released in Q1/2015. Evaluation kits are available for selected customers. Kit includes graphical diagnostics tool which is very useful to understand the network behav ...
Supported technologies in a nutshell
... Deployment scenarios According to general recommendations and best practices in network security NBA should be deployed together with traditional signature based solutions (anti-virus, anti-malware or intrusion detection and prevention) to monitor the network traffic for unknown or unusual deviation ...
... Deployment scenarios According to general recommendations and best practices in network security NBA should be deployed together with traditional signature based solutions (anti-virus, anti-malware or intrusion detection and prevention) to monitor the network traffic for unknown or unusual deviation ...
File - SME ASSOCIATES LLC
... It starts with the key user devices, utilizing a smart connection manager that will fully automate spectrum access to the point where the users will no longer have to think about what cellular operator, what Wi-Fi SSID, what Bluetooth connection is needed ...
... It starts with the key user devices, utilizing a smart connection manager that will fully automate spectrum access to the point where the users will no longer have to think about what cellular operator, what Wi-Fi SSID, what Bluetooth connection is needed ...
Chapter 5
... wait for the login prompt, and then record the network traffic that follows (usually capturing the password). By doing so, this tool can be used to historically capture certain types of traffic by simply leaving the tool running for a few days, and then the attacker just has to pick up the log file ...
... wait for the login prompt, and then record the network traffic that follows (usually capturing the password). By doing so, this tool can be used to historically capture certain types of traffic by simply leaving the tool running for a few days, and then the attacker just has to pick up the log file ...
[2017 New] Lead2pass 100% Valid 100
... protocol specific packets. Access lists can be used in a variety of situations when the router needs to be given guidelines for decision-making. These situations include: Filtering traffic as it passes through the router To control access to the VTY lines (Telnet) To identify "interesting" traffic t ...
... protocol specific packets. Access lists can be used in a variety of situations when the router needs to be given guidelines for decision-making. These situations include: Filtering traffic as it passes through the router To control access to the VTY lines (Telnet) To identify "interesting" traffic t ...
Presentation - Computer Science
... Implementing In-network aggregation in real environment for a Data-centric application ...
... Implementing In-network aggregation in real environment for a Data-centric application ...
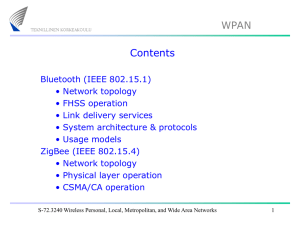
Lecture 2: WPAN
... modes serving as a personal area network (PAN) coordinator, a coordinator, or a device. Reduced-function devices (RFD) are intended for applications that are extremely simple. An FFD can talk to RFDs or other FFDs, while an RFD can talk only to an FFD. ...
... modes serving as a personal area network (PAN) coordinator, a coordinator, or a device. Reduced-function devices (RFD) are intended for applications that are extremely simple. An FFD can talk to RFDs or other FFDs, while an RFD can talk only to an FFD. ...
i Net2+ - Argon Audio
... C math library libm.so was added. Functions in this library provide common elementary mathematical functions and floating point environment routines defined by System V, ANSI C, POSIX, and so on. Additional functions in this library provide extended support for handling floating point exceptions. Fi ...
... C math library libm.so was added. Functions in this library provide common elementary mathematical functions and floating point environment routines defined by System V, ANSI C, POSIX, and so on. Additional functions in this library provide extended support for handling floating point exceptions. Fi ...
How The Internet Works - Directory | CS
... applications, however, typically use a client/server model for communications. A server is an application that offers a service to internet users; a client is a requester of a service. An application consists of both a server and a client part, which can run on the same or on different systems. User ...
... applications, however, typically use a client/server model for communications. A server is an application that offers a service to internet users; a client is a requester of a service. An application consists of both a server and a client part, which can run on the same or on different systems. User ...
Business Class DSL Routers
... SpeedStream Business Class DSL Routers are the complete DSL solution. Versatile, secure, and scalable — get a SpeedStream Business Class DSL Router and expand your DSL capabilities today! ...
... SpeedStream Business Class DSL Routers are the complete DSL solution. Versatile, secure, and scalable — get a SpeedStream Business Class DSL Router and expand your DSL capabilities today! ...
Sidh
... modeling the wireless medium; some only model the medium at a high level that is appropriate for roughly evaluating applications, others model the medium at the accuracy needed to evaluate low level protocols such as MAC. Finally, many simulators do not simulate the sensors, the physical phenomenon ...
... modeling the wireless medium; some only model the medium at a high level that is appropriate for roughly evaluating applications, others model the medium at the accuracy needed to evaluate low level protocols such as MAC. Finally, many simulators do not simulate the sensors, the physical phenomenon ...
AW+ Next-Generation Firewall Overview
... Allied Telesis NGFWs are a powerful and fully integrated solution that inspect and protect business data to ensure a secure online experience. Furthermore, they also provide comprehensive user connectivity through remote Virtual Private Network (VPN) access, advanced routing capabilities for Interne ...
... Allied Telesis NGFWs are a powerful and fully integrated solution that inspect and protect business data to ensure a secure online experience. Furthermore, they also provide comprehensive user connectivity through remote Virtual Private Network (VPN) access, advanced routing capabilities for Interne ...
Chapter 32 Security in the Internet: IPSec, SSL/TLS, PGP
... Under ideal circumstances, we would integrate IPSec’s protocols directly into IP itself. No extra headers or architectural layers are needed. 2- Bump in the stack: IPSec is made a separate layer between IP and data link layer. ...
... Under ideal circumstances, we would integrate IPSec’s protocols directly into IP itself. No extra headers or architectural layers are needed. 2- Bump in the stack: IPSec is made a separate layer between IP and data link layer. ...
FireWxNet: A Multi-Tiered Portable Wireless for Monitoring Weather
... protocols for communication, and were manually given IP addresses prior to deployment. ...
... protocols for communication, and were manually given IP addresses prior to deployment. ...
guest management - Washington Learning Source
... > Setup Connectivity without assistance? • Self Service Provisioning ...
... > Setup Connectivity without assistance? • Self Service Provisioning ...
LevelOne
... LevelOne 11g WLAN Outdoor AP / Bridge The LevelOne Outdoor Access Point is qualified for most Indoor/Outdoor applications. The waterproofed case with integrated heater secures function of the device in rough environments (WAB-1000H). The devices comply with IEEE 802.11b/g standard with a data transm ...
... LevelOne 11g WLAN Outdoor AP / Bridge The LevelOne Outdoor Access Point is qualified for most Indoor/Outdoor applications. The waterproofed case with integrated heater secures function of the device in rough environments (WAB-1000H). The devices comply with IEEE 802.11b/g standard with a data transm ...
Document
... ZigBee products are a combination of Application, ZigBee Logical, and ZigBee Physical device types Profiles may define specific requirements for this combination, but can also leave this up to manufacturers ...
... ZigBee products are a combination of Application, ZigBee Logical, and ZigBee Physical device types Profiles may define specific requirements for this combination, but can also leave this up to manufacturers ...
Home Networking activities in TTC
... ・Apparatus specification ・The surveillance/notice of NW connection / quality ・Apparatus state detection and a notice ...
... ・Apparatus specification ・The surveillance/notice of NW connection / quality ・Apparatus state detection and a notice ...
Firewalls
... – Complete view of the connections and app data – Filter bad data (viruses, Word macros) – Incoming packet is terminated and new packet is sent to internal network ...
... – Complete view of the connections and app data – Filter bad data (viruses, Word macros) – Incoming packet is terminated and new packet is sent to internal network ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.



![[2017 New] 100-105 New Questions For Passing The 100](http://s1.studyres.com/store/data/023784350_1-b9b9c774fb2f2bb6b07708217abac3c0-300x300.png)




![[2017 New] Lead2pass 100% Valid 100](http://s1.studyres.com/store/data/023631707_1-30e73a7c09fc0b272aa4be72fabb5404-300x300.png)